New findings suggest that Fortigate firewalls are at risk from remote code execution (RCE) attacks. A staggering 490,000 SSL VPN interfaces linked to these firewalls are accessible online, with approximately 69% still awaiting updates.
The security firm Bishop Fox created a proprietary exploit for CVE-2023-27997, a heap overflow in FortiOS—the operating system powering FortiGate firewalls. This particular vulnerability allows remote code execution.
CVE-2023-27997 causes a heap-based buffer leak in FortiGate’s SSL VPN module. Demonstrations have shown that attackers can exploit this weakness for pre-authentication remote code execution.
In order to address the disclosed risk, Fortinet has released updates and suggested an alternative solution. With the use of this misuse, users can alter the heap, establish a connection to a site under their control, get the BusyBox binary, and launch a virtual shell.
The steps to achieve this exploit closely resemble the procedure outlined in a blog post by Lexfo. It is possible for someone to execute these steps in about one second.
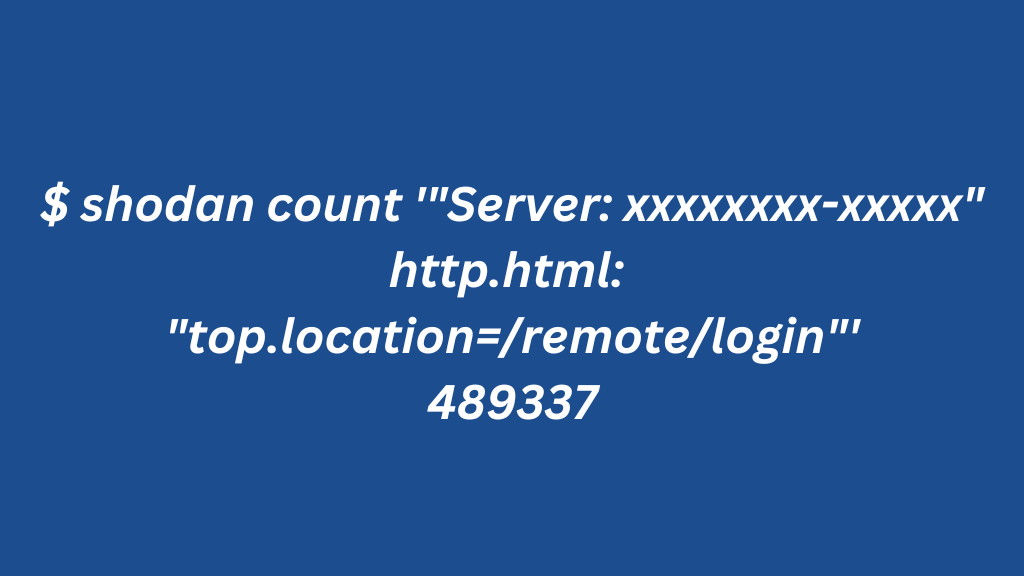
The following Shodan CLI search shows approximately 490,000 unsecured SSL VPN ports connected to The Fortigate Firewall.
Also Read: “Google Tackles 46 Vulnerabilities with Monthly Android Security Update”
In the past two months, Shodan has identified 335,923 devices that still need to patch the Last-Modified HTTP response header.
In the query below, we assumed that half of the devices installed in May had been patched. This assumption considers the presence of overlapping versions during that period. Additionally, all installations from June are assumed to be patched.
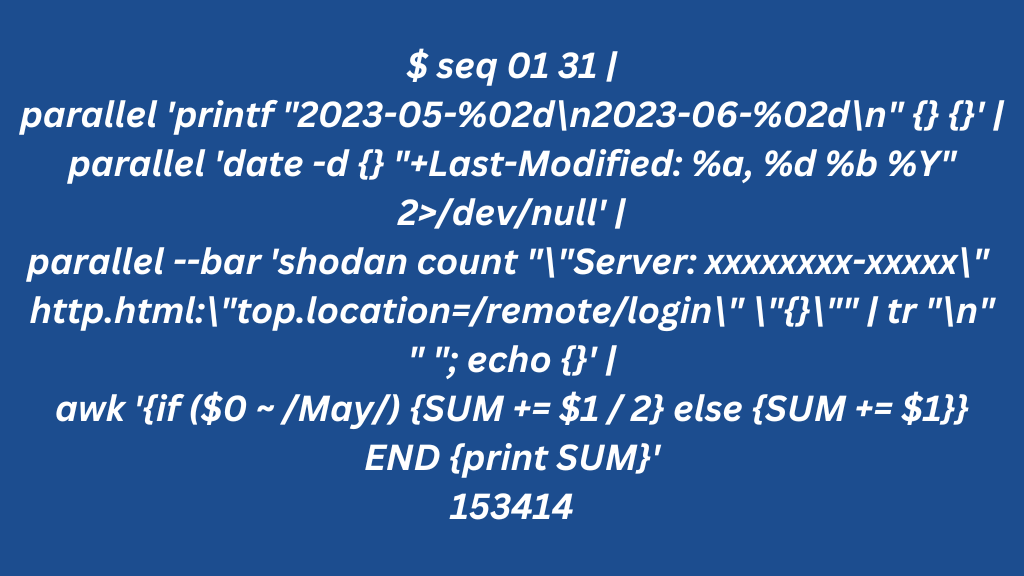
Based on these results, only 153,414 devices have received patches, leaving a worrying 69% (or 335,923 of 489,337) of devices unpatched.
The investigative team’s deeper examination revealed numerous installations of version 7 (released in early 2021) and a large number of version 6, which is gradually nearing the end of its lifecycle.






0 Comments