In its August 2023 Patch Tuesday release, Microsoft addressed 74 software vulnerabilities, a decline from the previous month’s 132 fixes. The update covers six critical and 67 important security vulnerabilities.
Two significant defense-in-depth updates were released, including one for Microsoft Office (ADV230003) and another for the Memory Integrity System Readiness Scan Tool (ADV230004).
Since the last update, Microsoft resolved 31 issues in its Chromium-based Edge browser and a notable side-channel vulnerability in certain AMD processor models (CVE-2023-20569, dubbed “Inception”).
Also Read: Allies or Adversaries? North Korea’s Cyber Espionage on Russian Soil
Noteworthy Details:
- The ADV230003 update pertains to a previously identified vulnerability, CVE-2023-36884. This security flaw, associated with remote code execution in both Office and Windows HTML, was exploited by the RomCom threat actor linked to Russia. The attacks were primarily against Ukraine and pro-Ukraine targets in Eastern Europe and North America. Microsoft assures that this new patch effectively disrupts the threat.
- ADV230004, the update for the Memory Integrity System Readiness scan tool, addresses a public bug. This tool initially lacked an RSRC section, which is essential for a module’s resource information.
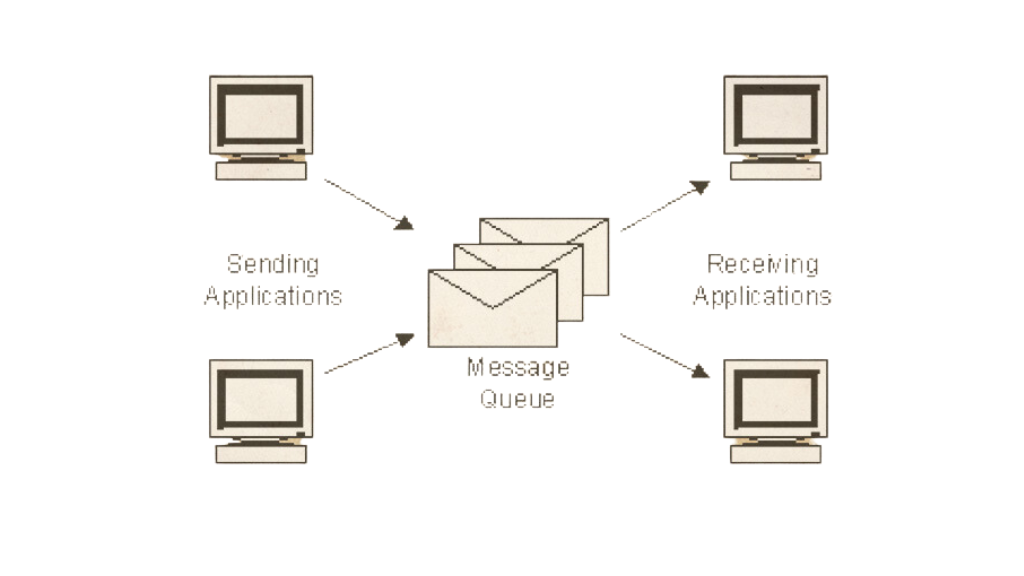
- Issues involving six denial-of-service (DoS) and two information disclosure vulnerabilities in MSMQ have also been addressed.
- Three significant vulnerabilities (CVE-2023-35388, CVE-2023-38182, and CVE-2023-38185) in the Exchange Server were resolved. Notably, the first two come with an “Exploitation More Likely” tag. Natalie Silva, Immersive Labs’ lead content engineer, commented on the need for adjacent attack vectors and valid exchange credentials for potential exploitation.
- A proof-of-concept (PoC) exploit concerning a DoS vulnerability in .NET and Visual Studio (CVE-2023-38180) was acknowledged by Microsoft. However, the tech giant clarified its limited functionality.
- Lastly, Microsoft released patches for five privilege escalation flaws in the Windows Kernel. These vulnerabilities can be exploited by local threat actors aiming for SYSTEM privileges.
This release further emphasizes Microsoft’s commitment to ensuring software security for its users and responding promptly to identified threats.






0 Comments