Cybersecurity experts have recently uncovered a novel mobile trojan that uses a unique method of communication.
This technique, termed as protobuf data serialization, enhances its capability to illicitly extract sensitive data from the targeted systems.
The report reveals that the malware, which they have named MMRat, first came to their attention in June 2023. The primary victims seem to be users in Southeast Asia. What’s notable is that when MMRat was initially detected, scanning platforms like VirusTotal did not recognize it as a threat.
MMRat boasts an extensive range of malicious capabilities. It can extract data related to the network, screen, and battery. Furthermore, it can pilfer contact lists, engage in keylogging, capture screen content in real-time, record and broadcast camera data, and even document screen data in textual formats. If needed, MMRat possesses the ability to delete itself.
Also Read: Deceptive AI Software Ads on Facebook: A Rising Cybersecurity Threat
Its feature to capture screen content in real-time stands out due to the need for high-speed data transfer, and this is where the prowess of the protobuf protocol comes into play. This custom protocol, designed specifically for data exfiltration, employs various ports and protocols to communicate with its command center.
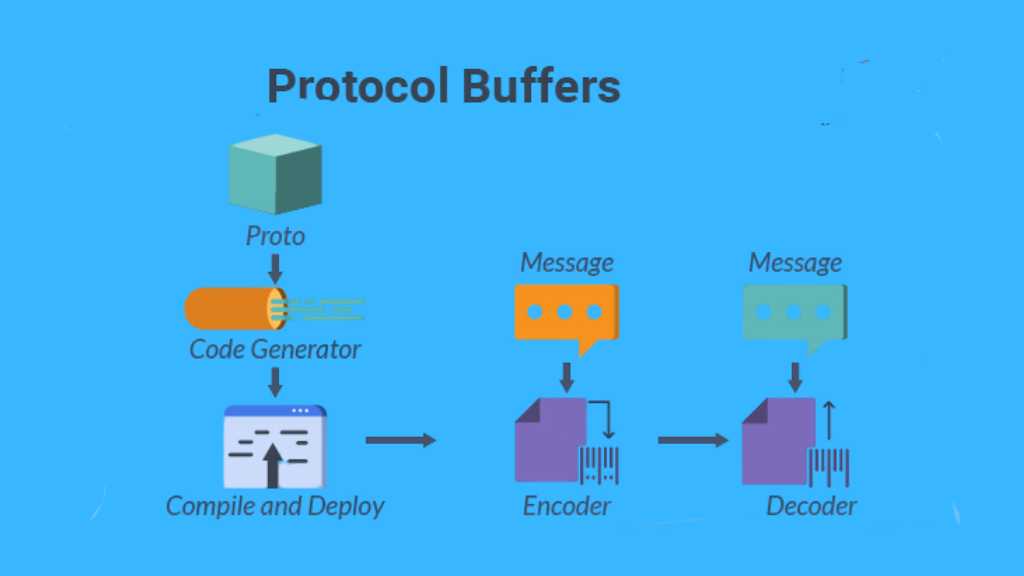
Highlighting its unique nature, the expert stated, “The command & control protocol stands out due to its tailored approach, built upon Netty (a network application framework) and the afore-mentioned Protobuf, enriched with meticulously crafted message structures. The communication with the command center is characterized by a comprehensive structure representing all message genres and the ‘oneof’ keyword specifying diverse data forms.”
The malevolent software was discovered masquerading on counterfeit mobile app platforms, often imitating government or dating applications. Though the level of sophistication in this malware is significant, it’s essential to note that these apps still request permissions from Android’s Accessibility Service – a common tell-tale sign of malicious intent.
Ultimately, the malware’s success is contingent upon the victim granting these permissions. If denied, MMRat becomes ineffective.






0 Comments