In networking and system administration, various tools help professionals analyze and troubleshoot network connections, scan for vulnerabilities, and perform various other tasks. Netstat, Nmap, and Netcat are popular tools with different purposes but similarities. In this post, we will compare Netstat vs. Nmap vs. Netcat, their differences, and use cases to help you understand which is best suited for your needs.
Netstat vs. Nmap vs. Netcat

Before diving into the details, let’s briefly explain what Netstat, Nmap, and Netcat are and how they function.
Also, Check: Nmap vs. Nessus: A Comprehensive Comparison
Netstat
Netstat, also known as “network statistics,” is a command-line tool that displays network connections and related statistics on a computer. It provides information about active connections, listening ports, routing tables, etc. Netstat is available on various operating systems, including Windows, Linux, and macOS.
The command-line network tool Netstat proves useful for troubleshooting. It actively displays the IP addresses of the networks recently connected with the target computer. Hackers commonly use it, granting them visibility into remote connections and potentially enabling them to target other vulnerable computers within the network.
Nmap
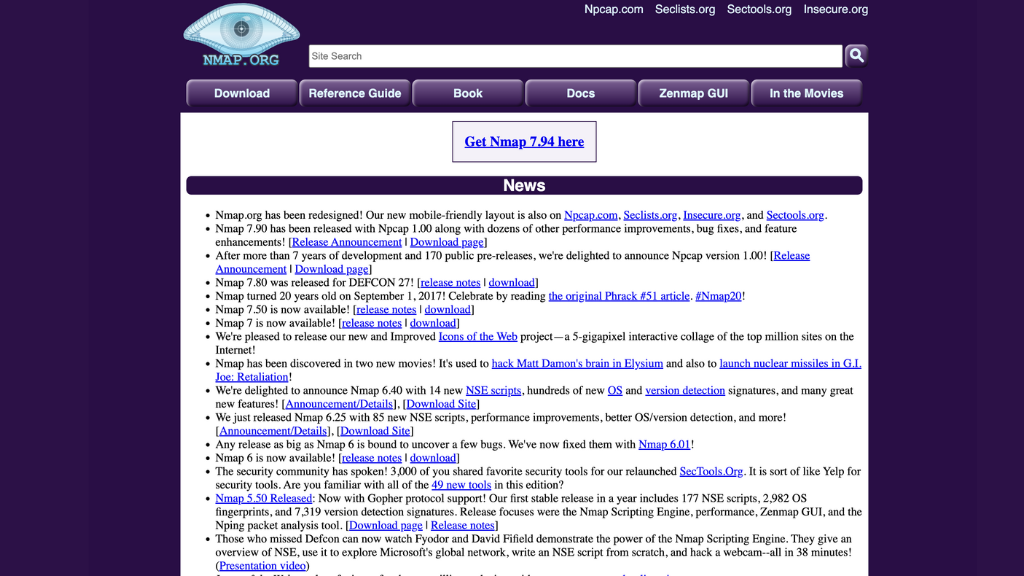
Nmap, short for “Network Mapper,” is a powerful open-source tool for network exploration and security auditing. It allows scanning and mapping network hosts, identifying open ports, services, and operating systems running on the network. Network administrators and security professionals widely use Nmap to assess the security posture of their systems.
Netcat
Netcat, or “nc,” is a versatile networking utility that can be a client or server for TCP and UDP connections. It can establish connections, listen for incoming connections, and transfer data between systems. Netcat is often used for port scanning, banner grabbing, file transfers, and creating network connections for testing or troubleshooting.
Netstat
Let’s start by examining Netstat in more detail.
Definition and Functionality
Netstat is primarily used to display active network connections, including the protocols, local and remote IP addresses, and the associated process or program using the connection. It can provide information on both TCP and UDP connections. Netstat also offers options for displaying routing tables, interface statistics, and multicast group memberships.
Features and Capabilities
Netstat offers several features and capabilities that make it a valuable tool for network analysis:
- Active connection monitoring: Netstat can display a list of active network connections, showing the source and destination IP addresses, ports, and the state of the connection.
- Listening ports: It can reveal the ports on which the system listens for incoming connections, allowing administrators to identify potential services or applications running on the system.
- Routing table information: Netstat can provide details about the routing table, helping administrators understand how network traffic is routed.
- Interface statistics: It can display statistics related to network interfaces, such as the number of packets sent and received, errors, and other metrics.
Use Cases and Benefits.
Netstat is commonly used for various purposes, including:
- Monitoring network connections: Network administrators can utilize Netstat to monitor active connections, identify which processes or programs use specific connections, and detect any unusual or unauthorized connections.
- Troubleshooting network issues: By examining the state of network connections, listening ports, and routing information, Netstat can assist in diagnosing and troubleshooting network-related problems.
- Identifying network activity: Netstat allows administrators to track network activity, providing insights into network traffic patterns, usage statistics, and potential security breaches.
Nmap
Moving on, let’s explore the features and applications of Nmap.
Definition and Functionality
Nmap is a highly versatile tool that enables network scanning, port discovery, and host profiling. It uses raw IP packets to determine which hosts are available on the network, what services and operating systems they are running, and which ports are open.
Features and Capabilities
Nmap offers an extensive range of features and capabilities:
- Host discovery: Nmap can discover hosts on a network by sending special packets and analyzing the responses.
- Port scanning: It can scan target hosts to determine which ports are open, closed, or filtered by firewalls.
- Service and version detection: Nmap can identify the services running on the open ports and attempt to determine their versions.
- Operating system detection: It can fingerprint the operating systems running on the target hosts based on various characteristics.
- Scripting engine: Nmap includes a powerful scripting engine called NSE (Nmap Scripting Engine), which allows users to write and execute scripts for advanced network scanning and vulnerability detection.
Use Cases and Benefits.
Nmap is widely used for the following purposes:
- Network exploration: Nmap enables administrators to discover hosts, identify available services, and map the network topology.
- Security auditing: By scanning for open ports and identifying vulnerable services, Nmap helps assess the security posture of network systems.
- Intrusion detection: Nmap can be used as part of an intrusion detection system to monitor and alert on unexpected network activity.
- Firewall testing: It assists in evaluating the effectiveness of firewall configurations by scanning for open and filtered ports.
- Network inventory management: Nmap can aid in keeping track of devices connected to the network and their characteristics.
Netcat

Now, let’s delve into the features and use cases of Netcat.
Definition and Functionality
Netcat is a command-line networking utility that can create TCP or UDP connections, listen for incoming connections, and transfer data between systems. It operates as a simple but powerful tool for network communication.
Features and Capabilities
Netcat offers a range of features and capabilities, including:
- Port scanning: Netcat can scan for open ports on a target system, similar to Nmap.
- File transfer: It allows the transfer of files between systems using TCP or UDP connections.
- Remote shell access: Netcat can establish a shell session on a remote system, providing remote command execution capabilities.
- Port forwarding: It can forward network connections from one system to another, enabling proxying or tunneling.
Use Cases and Benefits
Netcat finds applications in various scenarios:
- Port scanning and banner grabbing: Like Nmap, Netcat can scan for open ports on target systems and retrieve banners or service information.
- File transfers: It provides a quick and efficient method of transferring files between systems, making it useful for backup purposes or sharing files over a network.
- Network testing and troubleshooting: Netcat allows users to create network connections for testing purposes, simulate client-server interactions, and troubleshoot network-related issues.
- Remote administration: By establishing remote shell sessions, Netcat facilitates remote administration and execution of commands on target systems.
Comparison Between Netstat, Nmap, and Netcat
While Netstat, Nmap, and Netcat serve different purposes, they can complement each other in specific scenarios. Here’s a comparison of these tools:
- Functionality: Netstat primarily displays active connections and network statistics, while Nmap specializes in network scanning and host profiling. Netcat excels at creating network connections and transferring data.
- Level of detail: Netstat provides information about individual connections and basic network statistics, whereas Nmap offers in-depth information about hosts, ports, services, and operating systems. Netcat operates at a lower level, enabling raw data transfer.
- Ease of use: Netstat is relatively straightforward to use, as it mainly involves displaying information. Nmap and Netcat require more advanced knowledge and command-line usage.
- Use case overlap: While Nmap and Netcat can perform port scanning, Nmap provides more comprehensive scanning capabilities, including service detection and operating system fingerprinting. Netcat is simpler and focused on network communication.
Conclusion
Netstat, Nmap, and Netcat are powerful networking tools for network analysis, security auditing, and communication. Understanding their functionalities and use cases can help professionals leverage them effectively to troubleshoot issues, secure networks, and streamline network-related tasks.
When used together, these tools can provide a comprehensive view of a network’s security posture and help identify potential vulnerabilities.
For professional cybersecurity services and expertise, consider contacting NextDoorSec, a leading cybersecurity firm.






0 Comments