Researchers from four renowned U.S. universities have unveiled a novel GPU side-channel attack. This method uses data compression techniques to extract critical visual information from contemporary graphic cards, especially when browsing web pages.
This new technique, termed ‘GPU.zip,’ was demonstrated to be effective by the researchers. They used the Chrome browser to launch cross-origin SVG filter pixel-extraction attacks to demonstrate its capabilities.
Even though susceptible video card makers were made aware of the flaw in March 2023, by September 2023, no fixes had been offered by impacted GPU vendors like AMD, Apple, Arm, NVIDIA, Qualcomm, or even Google Chrome. This intriguing discovery is detailed in a paper crafted by specialists.
Usually, data compression generates unique data-centric DRAM traffic and cache usage patterns. These can potentially be exploited to expose concealed data. Hence, to avoid this, software typically disables compression when managing confidential data.
The creators of GPU.zip pointed out that modern graphic processors, particularly the ones made by Intel and AMD, frequently compress data even when not specifically requested.
Such a practice is adopted by modern GPUs to optimize performance, allowing memory bandwidth conservation and performance enhancement without software’s intervention.
The researchers took advantage of this compression technique, which frequently lacks documentation and varies between vendors, to steal graphic information from GPUs.
Also Read: Facebook Subject to Lawsuit over Alleged Discriminatory Ads in California
Their experiment showed an attack that could extract pixel details through web browsers across different devices and GPU designs. An illustration of their technique involved extracting a user’s name from a Wikipedia iframe, achievable in 30 minutes for Ryzen and 215 minutes for Intel GPUs, with precision rates of 97% and 98.3%, respectively.
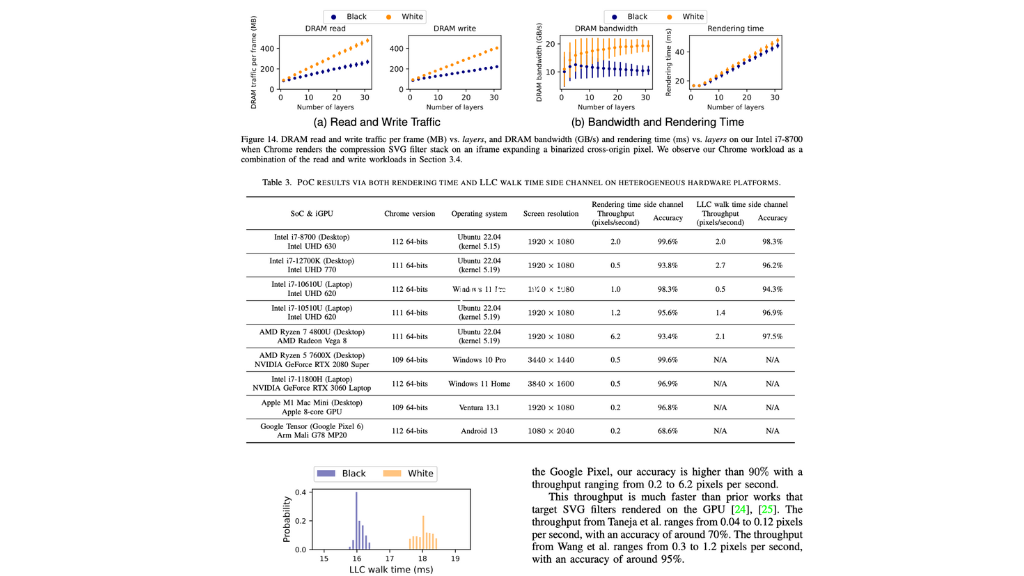
Image Source: hertzbleed.com
The plugin displays a cross-origin webpage with binary distillation of its pixels, displaying it in two unique colors.
These pixels are then made larger, and a special set of SVG filters is used to create textures that are either compressible or not. By gauging the rendering duration of these textures, the initial color or state of the desired pixel can be inferred.
This approach bears semblance to the “Hot Pixels” attack, which also uses SVG filters and JavaScript to discern pixel colors based on computation times. But while Hot Pixels takes advantage of data-centric processing intervals on modern processors, GPU.zip takes advantage of the unexplored possibilities of GPU data compression for comparable results.
Nearly all leading GPU producers, including AMD, Apple, Arm, Intel, Qualcomm, and NVIDIA, are susceptible to GPU.zip, though the degree of vulnerability varies.
The lack of remedial action from these vendors, especially in tweaking their compression methods to exempt confidential scenarios, elevates the associated risks.
Despite GPU.zip having the potential to compromise numerous electronic devices globally, the intricacy and time needed to execute the attack curtail its immediate threat. Additionally, web platforms prohibiting cross-origin iframe embedding remain impervious to this and analogous side-channel assaults.
The researchers pointed out in their FAQ that many security-conscious websites are already resistant to such intrusions due to their refusal to allow embedding by external sites.
It’s noteworthy that browsers like Firefox and Safari exhibit incompatibility with the prerequisites for GPU.zip to function effectively, offering users a degree of protection against this newfound threat.






0 Comments