In today’s increasingly interconnected world, ensuring the security of digital systems and networks is paramount. As companies strive to protect their valuable data, two commonly employed methodologies come into play: penetration testing and security testing. While they share the common goal of uncovering vulnerabilities and weaknesses, these approaches have distinct differences. This post sheds light on the contrasting characteristics of penetration vs. security testing, providing insights to help you find which approach best suits your specific needs.
Penetration Testing vs. Security Testing
What is Penetration Testing?

Penetration testing, often called “pen testing,” is a systematic approach to evaluating the security of an organization’s systems, networks, or applications. It involves simulating real-world attacks to identify potential vulnerabilities malicious actors could exploit.
Penetration testing can be considered a type of security audit. By emulating the tactics and techniques of hackers, penetration testing helps organizations proactively identify and remediate security weaknesses.
Importance of Penetration Testing
Penetration testing plays a crucial role in strengthening an organization’s security posture. Identifying vulnerabilities before they can be exploited enables businesses to implement appropriate security measures and safeguards.
Penetration testing helps organizations stay one step ahead of cyber threats, safeguarding sensitive data and mitigating the risk of breaches or unauthorized access.
Benefits of Penetration Testing
Penetration testing offers several key benefits. Firstly, it provides a comprehensive assessment of an organization’s security defenses, uncovering vulnerabilities that might have been overlooked.
Secondly, it helps validate the effectiveness of existing security controls and measures. Additionally, penetration testing assists in meeting regulatory compliance requirements and industry standards. It helps organizations maintain a robust security infrastructure and instill confidence in stakeholders.
What is Security Testing?
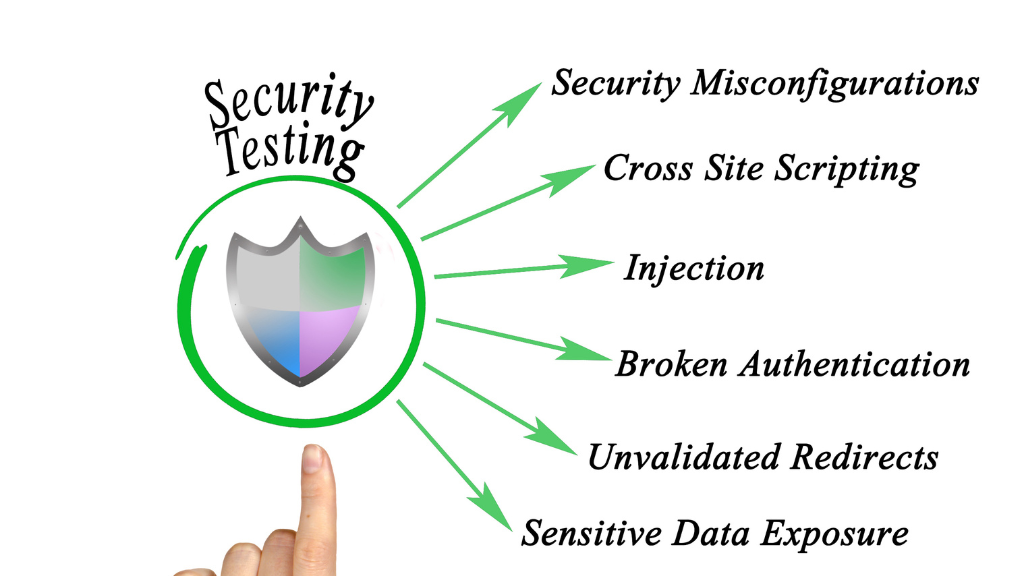
Security testing assesses the effectiveness of an organization’s security controls, policies, and procedures. It encompasses a broader range of activities that evaluate the overall security posture, including risk assessment, vulnerability scanning, code review, access controls, and more.
Security testers aim to ensure that systems and applications are adequately protected against potential threats.
For example, DAST (Dynamic Application Security Testing). It is a type of security testing that focuses on evaluating the security of an application or software in its running state. DAST complements other security testing techniques, such as Static Application Security Testing (SAST), which analyzes the application’s source code without executing it.
Importance of Security Testing
In a world where cyber threats continue to evolve, security testing is vital to safeguarding an organization’s critical assets. It helps identify vulnerabilities and weaknesses in the security infrastructure, ensuring appropriate measures are in place to protect sensitive information.
Security testing also aids in compliance with industry regulations and standards, instilling trust among customers, partners, and stakeholders.
Benefits of Security Testing
Security testing offers numerous benefits to organizations. It helps identify and address security flaws and vulnerabilities, minimizing the risk of data breaches or unauthorized access.
Organizations can prevent financial losses, reputational damage, and legal implications by implementing adequate security controls. Security testing also enhances customer trust, demonstrating a commitment to safeguarding sensitive data and maintaining a secure environment.
Differences between Penetration Testing vs. Security Testing
Focus and Objectives
Penetration testing primarily focuses on identifying vulnerabilities through simulated attacks and attempts to exploit them actively. It aims to evaluate the resilience of an organization’s defenses against real-world threats.
On the other hand, security testing takes a broader perspective, assessing the overall security controls and measures to ensure compliance, risk mitigation, and adherence to best practices.
Scope and Coverage
Penetration testing typically has a narrower scope, targeting specific systems, networks, or applications. It aims to uncover vulnerabilities within the defined scope.
In contrast, security testing encompasses a more comprehensive assessment of an organization’s security posture, including policies, procedures, access controls, and other security measures.
Methodology and Techniques
Penetration testing relies on a simulated attacker’s mindset, utilizing various techniques and tools to identify and exploit vulnerabilities. It often involves manual testing, ethical hacking, and social engineering to mimic real-world attack scenarios.
On the other hand, security testing employs automated tools, code reviews, vulnerability assessments, and risk analysis to evaluate the overall security of systems and applications.
Tools and Technologies
Penetration testing commonly utilizes specialized tools and frameworks, such as network scanners, vulnerability scanners, password-cracking tools, and exploit frameworks. These tools assist in identifying and exploiting vulnerabilities.
Security testing employs a broader range of tools, including vulnerability scanners, intrusion detection systems, firewalls, secure coding practices, and encryption technologies, to comprehensively evaluate security controls.
Both use performance testing in one way or another through a particular tester to test different software.
Reporting and Deliverables
Penetration testing typically provides detailed reports highlighting discovered vulnerabilities, their potential impact, and actionable recommendations for remediation. It focuses on specific vulnerabilities and their exploitation paths.
Security testing, on the other hand, gives:
- A comprehensive assessment of a company’s security posture.
- Offering insights into overall risk levels.
- Compliance gaps.
- Recommendations for enhancing the security infrastructure.
Which Testing Approach to Choose?
Assessing Your Security Needs
Assessing your organization’s specific security needs is crucial to determine the most appropriate testing approach. Consider your systems’ criticality, data sensitivity, industry regulations, and compliance requirements.
Regulatory Compliance
Compliance with specific security standards may be mandatory if your organization operates in a regulated industry. In such cases, security testing is crucial in ensuring adherence to rules and the industry’s best techniques.
Budget and Resources

Consider the resources available to conduct testing. Penetration testing often requires specialized expertise and manual testing efforts, which can be more resource-intensive than security testing.
Assess your budget and resource constraints when deciding between the two approaches.
Industry Best Practices
Research industry-specific best practices and recommendations. This can help guide your decision on the most suitable testing approach based on the prevailing standards within your industry.
Conclusion
Penetration and security testing are both crucial components of a comprehensive cybersecurity strategy. While they share the common goal of assessing and enhancing the security of systems and applications, they have distinct focuses and methodologies.
For reliable and effective penetration testing and security testing services, consider partnering with NextDoorSec, a reputable cybersecurity firm.
FAQs
1. What is the difference between security and penetration testing?
Security testing is a broad term encompassing various techniques to identify and address vulnerabilities in a system or network. Penetration testing, or pen testing, is a specific type of security testing where testers simulate real-world attacks to identify specific vulnerabilities and security weaknesses in a system.
2. What is the difference between a penetration test and a security audit?
A penetration test actively exploits vulnerabilities in a system to determine its defenses against attacks. In contrast, a security audit is a comprehensive review and analysis of a system’s security measures, including policies, procedures, and configurations, often against a set of established standards or guidelines. Penetration testing is more hands-on and attack-focused, while security audits are broader and more compliance and policy-oriented.
3. Is penetration testing part of cybersecurity?
Yes, penetration testing is a critical component of cybersecurity. It involves simulating cyber attacks on systems, networks, or applications to identify and address security vulnerabilities before they can be exploited by malicious actors.
4. What is the difference between a security assessment and a penetration test?
A security assessment is a broad evaluation of an organization’s information security posture, including policies, procedures, controls, and technologies. It identifies vulnerabilities and risks but doesn’t typically involve active exploitation of vulnerabilities. A penetration test, on the other hand, is a more focused, hands-on approach specifically designed to exploit vulnerabilities in the system to understand the level of risk and the potential impact of an attack.
5. What is Dynamic Application Security Testing (DAST)?
Dynamic Application Security Testing (DAST) is a testing process that identifies security vulnerabilities in a running web application. It simulates external attacks and looks for issues like SQL injection and cross-site scripting without needing access to the source code.
6. What is Penetration Testing (PenTesting)?
Penetration Testing, or PenTesting, is a simulated cyber attack against a system to identify and exploit vulnerabilities. It aims to uncover security weaknesses through methods like attempting to breach application systems, APIs, servers, and other points of exposure.






0 Comments