Over the past weekend, there have been widespread online whispers about a potential zero-day security flaw associated with Signal Messenger’s ‘Generate Link Previews’ feature. However, Signal has declared there’s no proof to substantiate this alleged vulnerability.
These concerns gained traction after several informants relayed to BleepingComputer and posted tweets suggesting a newfound vulnerability might enable malicious actors to gain full control of affected devices.
In light of these claims, Signal proactively reached out to the public through a Twitter post. Their statement clarifies: “In response to the circulated reports hinting at a Signal 0-day flaw, we’ve conducted a thorough inquiry. As of now, there’s no solid evidence supporting the existence of such a vulnerability. Furthermore, no details regarding this have been channeled through our formal communication platforms.”
Also Read: What the Hollywood Strike Teaches Cybersecurity About AI Integration
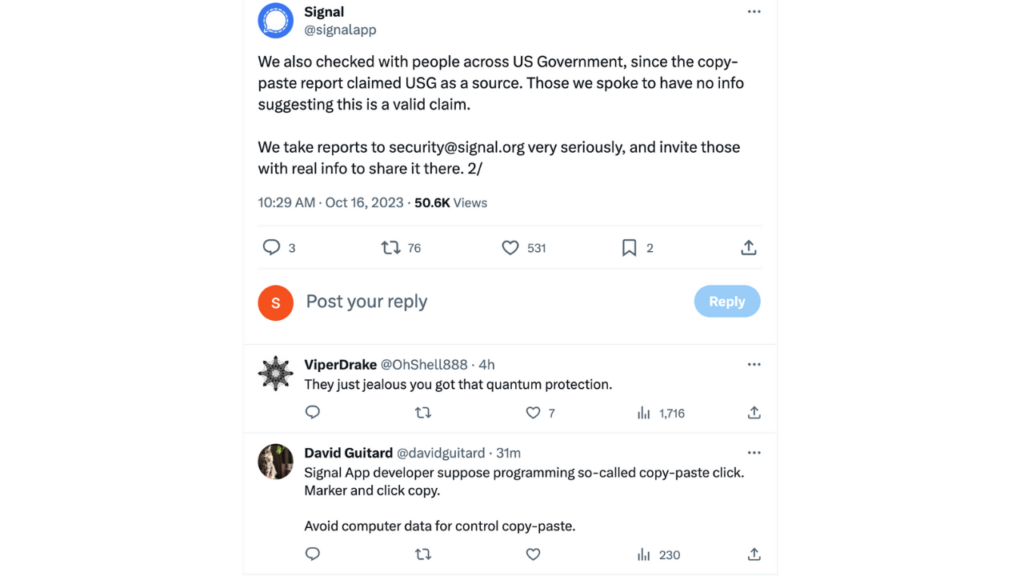
The statement also highlights Signal’s consultation with representatives from the US Government, especially since the initial reports had insinuated their involvement. The officials Signal conferred with didn’t affirm these claims either.
The rapid spread of this rumor in the cybersecurity domain on Saturday can be attributed, in part, to unnamed US Government informants. These informants advised that users could potentially counteract the supposed vulnerability by deactivating the ‘Generate Link Previews’ function on Signal. Despite hearing this from multiple individuals who cited the same sources, BleepingComputer hasn’t been able to validate the accuracy of such assertions.
While Signal reaffirms the lack of tangible evidence pointing to a new zero-day flaw, they encourage anyone with credible and substantial information to get in touch with their security division. Given the nature of the situation and the proposed workaround of deactivating the Link Previews function, users might consider toggling off this feature as a precautionary measure until more concrete information surfaces.






0 Comments