Intro
Hello there and welcome to my first ever write-up.
Recently I’ve been spending a lot of time on TryHackMe; it’s a really addictive platform for studying and practising your hacking skills at the same time. Instead of posting commands and theories, I’ve decided to do write-ups, as it provides much more value. So let’s get started. Here’s a link to the box.
Steel Mountain is a Windows themed machine from TryHackMe, based on the Mr Robot Tv series (my all-time favourite show). The official walkthrough is provided with Metasploit, which makes it pretty easy to root. However, we’ll be doing it all manually today, because you’re not able to use auto-exploit tools on the OSCP exam.
This makes you understand how it all works behind the scenes, so when you get stuck with scripts doing it all automatically, you can fall back to the manual way of things. I’ve kept the methodology simple to Enumeration, Exploitation & Privilege Escalation.
Enumeration
Running a Nmap scan:
┌──(kali㉿kali)-[~] └─$ nmap -A -Pn -v $IP
PORT STATE SERVICE VERSION 80/tcp open http Microsoft IIS httpd 8.5 | http-methods: | Supported Methods: OPTIONS TRACE GET HEAD POST |_ Potentially risky methods: TRACE |_http-server-header: Microsoft-IIS/8.5 |_http-title: Site doesn't have a title (text/html). 135/tcp open msrpc Microsoft Windows RPC 139/tcp open netbios-ssn Microsoft Windows netbios-ssn 445/tcp open microsoft-ds Microsoft Windows Server 2008 R2 - 2012 microsoft-ds 3389/tcp open ssl/ms-wbt-server? | ssl-cert: Subject: commonName=steelmountain | Issuer: commonName=steelmountain | Public Key type: rsa | Public Key bits: 2048 | Signature Algorithm: sha1WithRSAEncryption | Not valid before: 2020-10-11T19:04:29 | Not valid after: 2021-04-12T19:04:29 | MD5: cf4c 483f 7654 c778 e6b9 0144 1de0 18c9 |_SHA-1: ed4f 6cac 8059 d465 9e7b 7730 8ac4 56a4 67df d29c |_ssl-date: 2021-02-05T15:22:17+00:00; -1s from scanner time. 8080/tcp open http HttpFileServer httpd 2.3 |_http-favicon: Unknown favicon MD5: 759792EDD4EF8E6BC2D1877D27153CB1 | http-methods: |_ Supported Methods: GET HEAD POST |_http-server-header: HFS 2.3 |_http-title: HFS / 49152/tcp open msrpc Microsoft Windows RPC 49153/tcp open msrpc Microsoft Windows RPC 49154/tcp open msrpc Microsoft Windows RPC 49155/tcp open msrpc Microsoft Windows RPC 49157/tcp open msrpc Microsoft Windows RPC Service Info: OSs: Windows, Windows Server 2008 R2 - 2012; CPE: cpe:/o:microsoft:windows Host script results: |_clock-skew: mean: -1s, deviation: 0s, median: -1s | nbstat: NetBIOS name: STEELMOUNTAIN, NetBIOS user:
I like including the -v flag for verbosity, as the scan continues and gives me some results, I’m able to probe around to see for anything interesting. On port 80 we find a Microsoft web server that contains a random picture of someone from the Mr Robot series.
Running dirbuster doesn’t give us anything interesting.
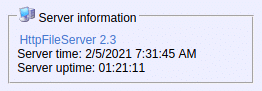
When we explore the web server on port 8080, we find a http file server running on version 2.3, left below we see “Server Information” that contains a link to the vendor’s website:

Exploitation
Let’s search if this version of the webserver is vulnerable:
----------------------------------------------------------------------------------------- --------------------------------- Exploit Title | Path ----------------------------------------------------------------------------------------- --------------------------------- Rejetto HttpFileServer 2.3.x - Remote Command Execution (3) | windows/webapps/49125.py ----------------------------------------------------------------------------------------- --------------------------------- Shellcodes: No Results
Copy the exploit to a local path & check its usage. After reading through, we need a reverse shell payload, I’ll use Powershell, as I haven’t tested it much. Check below for the code & make sure you change the IP & port values with your own.
After configuring the payload, it’s time to start our Netcat listener (need to sudo if the port is and below 1023) and our HTTP server to download & run the reverse shell binary on the target.
┌──(kali㉿kali)-[~] └─$ sudo nc -nlvp 443 listening on [any] 443 ... ┌──(kali㉿kali)-[~] └─$ python3 -m http.server 5300
Now that we’ve set up everything, it’s time to run our exploit & catch the shell with our listener (this one-liner runs in Powershell’s memory):
Privilege Escalation
We’re in now, which means it’s time for some more enumeration, we need to find weak points and identify vulnerable configurations. I always start by finding who I am and what my privileges are.
whoami
Bypass traverse checking means that we can only view certain files in certain folders without being able to list their contents, we’re only able to “traverse” to the file to which we have access set previously by the admin or system.
Other (hidden) users
Let’s view the other existing users in the system, the -Force command lets us see the hidden files too:
Any users in the Administrators group
We don’t find any of the users in the Administrators group.
Let’s check Winlogon for saved credentials
HKEY_LOCAL_MACHINE\Software\Microsoft\Windows NT\CurrentVersion\winlogon Userinit REG_SZ C:\Windows\system32\userinit.exe, LegalNoticeText REG_SZ Shell REG_SZ explorer.exe LegalNoticeCaption REG_SZ DebugServerCommand REG_SZ no ForceUnlockLogon REG_DWORD 0x0 ReportBootOk REG_SZ 1 VMApplet REG_SZ SystemPropertiesPerformance.exe /pagefile AutoRestartShell REG_DWORD 0x1 PowerdownAfterShutdown REG_SZ 0 ShutdownWithoutLogon REG_SZ 0 Background REG_SZ 0 0 0 PreloadFontFile REG_SZ SC-Load.All PasswordExpiryWarning REG_DWORD 0x5 CachedLogonsCount REG_SZ 10 WinStationsDisabled REG_SZ 0 PreCreateKnownFolders REG_SZ {A520A1A4-1780-4FF6-BD18-167343C5AF16} DisableCAD REG_DWORD 0x1 scremoveoption REG_SZ 0 ShutdownFlags REG_DWORD 0x7 AutoLogonSID REG_SZ S-1-5-21-3029548963-3893655183-1231094572-1001 LastUsedUsername REG_SZ bill DefaultUserName REG_SZ bill DefaultPassword REG_SZ PMBAf5KhZAxVhvqb AutoAdminLogon REG_SZ 1 PS C:\Users\bill\Downloads> Get-ItemProperty -Path 'Registry::HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\WinLogon' | select "Default*"
DefaultUserName DefaultPassword --------------- --------------- bill PMBAf5KhZAxVhvqb
We found Bill’s password: PMBAf5KhZAxVhvqb
Although we have an open RDP port (3389), I couldn’t connect, not sure why.
Tip: HKLM keys are run (if required) every time the system is booted while HKCU keys are only executed when a specific user logs on to the system.
Check for weak folder permissions
We’ll find all weak folder permissions per drive with accesschk.exe downloaded from the official Microsoft website. You can use your apache server or an smb-server to transfer it. (took me ~1 min, be patient)
RW C:\ RW C:\ProgramData\Amazon RW C:\ProgramData\IObit RW C:\ProgramData\Oracle RW C:\ProgramData\ProductData RW C:\ProgramData\{FD6F83C0-EC70-4581-8361-C70CD1AA4B98} RW C:\ProgramData\Amazon\EC2-Windows RW C:\ProgramData\Amazon\Ec2Config RW C:\ProgramData\Amazon\SSM RW C:\ProgramData\Amazon\EC2-Windows\Launch RW C:\ProgramData\Amazon\EC2-Windows\Launch\Config RW C:\ProgramData\Amazon\EC2-Windows\Launch\Module RW C:\ProgramData\Amazon\EC2-Windows\Launch\Scripts RW C:\ProgramData\Amazon\EC2-Windows\Launch\Settings RW C:\ProgramData\Amazon\EC2-Windows\Launch\Sysprep RW C:\ProgramData\Amazon\EC2-Windows\Launch\Module\Scripts RW C:\ProgramData\Amazon\Ec2Config\Logs RW C:\ProgramData\Amazon\Ec2Config\Monitor RW C:\ProgramData\Amazon\SSM\InstanceData RW C:\ProgramData\Amazon\SSM\Logs RW C:\ProgramData\IObit\Advanced SystemCare RW C:\ProgramData\IObit\ASCDownloader RW C:\ProgramData\IObit\IObit Uninstaller RW C:\ProgramData\IObit\IObitRtt RW C:\ProgramData\IObit\Advanced SystemCare\Homepage Protection RW C:\ProgramData\IObit\Advanced SystemCare\smBootTime RW C:\ProgramData\IObit\Advanced SystemCare\Startup Manager RW C:\ProgramData\IObit\IObit Uninstaller\database ... ----------------- -d Only process directories or top level key -q Omit banner -s Recurse -u Suppress errors -v Verbose (includes Windows Vista Integrity Level) -w Show only objects that have write access
The IObit software gets my attention immediately, because it’s unusual (after seeing some defaults, you’ll get used to it). Searching again for weak file permissions with “
.\accesschk.exe -uwqs Users c:\“. gives me the same results.
Check for running processes/services
Image Name PID Services ========================= ======== ============================================ ... services.exe 640 N/A lsass.exe 648 SamSs svchost.exe 704 BrokerInfrastructure, DcomLaunch, LSM, PlugPlay, Power, SystemEventsBroker svchost.exe 732 RpcEptMapper, RpcSs ASCService.exe 824 AdvancedSystemCareService9 dwm.exe 836 N/A svchost.exe 948 Dhcp, EventLog, lmhosts, Wcmsvc ...
Check for process owner of the service
This one-liner returns the process owner without admin rights, if something is blank under owner it’s probably running as SYSTEM, NETWORK SERVICE, or LOCAL SERVICE.
Name Handle Owner ---- ------ ----- System Idle Process 0 System 4 smss.exe 360 csrss.exe 492 csrss.exe 544 wininit.exe 572 winlogon.exe 580 services.exe 640 lsass.exe 648 ASCService.exe 824 dwm.exe 836 spoolsv.exe 1208 amazon-ssm-agent.exe 1252 LiteAgent.exe 1324 LiveUpdate.exe 1452 Ec2Config.exe 1664 WmiPrvSE.exe 2368 taskhostex.exe 2628 bill explorer.exe 2692 bill hfs.exe 2504 bill msdtc.exe 3488 powershell.exe 3636 bill powershell.exe 3660 bill conhost.exe 3668 bill conhost.exe 3692 bill
Query the service
We saw AdvancedSystemCareService almost on every check, let’s query the service to check out its config:
[SC] QueryServiceConfig SUCCESS SERVICE_NAME: AdvancedSystemCareService9 TYPE : 110 WIN32_OWN_PROCESS (interactive) START_TYPE : 2 AUTO_START ERROR_CONTROL : 1 NORMAL BINARY_PATH_NAME : C:\Program Files (x86)\IObit\Advanced SystemCare\ASCService.exe LOAD_ORDER_GROUP : System Reserved TAG : 1 DISPLAY_NAME : Advanced SystemCare Service 9 DEPENDENCIES : SERVICE_START_NAME : LocalSystem
The binary path name is unquoted and it contains spaces. So windows will first try to run Advanced.exe before the actual executable. Therefor we need to place our payload into C:\Program Files (x86)\IObit\ & rename it to Advanced.exe. Afterwards restart the service, because it’s currently running as seen above. We also confirmed we have read & write (RW) access to the folder above with accesschk.exe.
Let’s create our second reverse shell payload using msfvenom, name it Advanced.exe, transfer to the target machine using certutil.exe and start a listener on the specified port. Stop the service, make sure it’s stopped with Get-Service & start it again:
Now you should have a shell as SYSTEM.






0 Comments