In a compelling follow-up to a 2008 incident where MIT students discovered a loophole to ride Boston’s subway for free, a group of teens has uncovered similar vulnerabilities in the Massachusetts Bay Transit Authority (MBTA) system. Matty Harris and Zachary Bertocchi, inspired by a Wikipedia article recounting the MIT hack, began investigating if the same exploit could be used today. To their astonishment, they found that the security flaws remained unpatched.
Back in 2008, MIT hackers manipulated the Charle Ticket magstripe paper cards to gain free rides. While these cards were phased out in 2021, the teenage quartet, which also includes Noah Gibson and Scott Campbell, progressed this research to hack the RFID-based CharlieCard that replaced the older tickets.
Also Read: Microsoft Responds to Threat Landscape: August 2023 Patch Insights
They succeeded in reverse-engineering the CharlieCard, allowing them to add funds or change its designation to various types, like student or employee cards, granting unlimited rides. They even crafted a desktop device and an Android app to alter the card’s value.
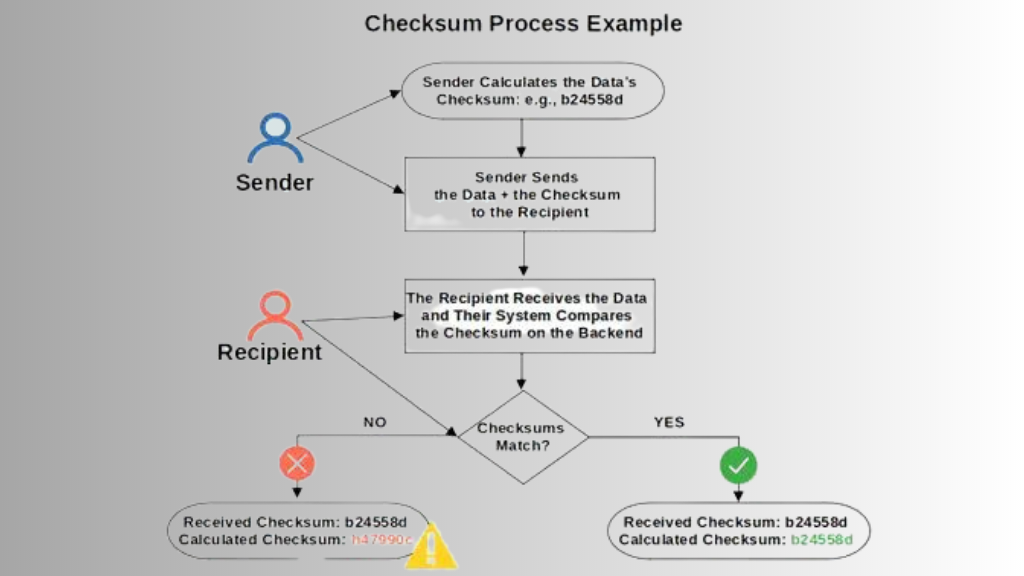
Unlike traditional cards, CharlieCards store about a kilobyte of data, including their balance. The teens were able to decipher the system’s “checksum” mechanism that validates the card balance and modify the card’s monetary value accordingly.
In December of the preceding year, an MIT graduate, Bobby Rauch, unveiled a cloning technique for the CharlieCards. Collaborating with Rauch, the teens introduced their more advanced findings to the MBTA. Recognizing the value of friendly hackers, the MBTA started a vulnerability disclosure program. In a meeting, the agency requested the teens withhold their technique for 90 days. It seems the MBTA is working on detecting altered cards, but, as Harris mentioned, only a few hacked cards have been identified.
In contrast to the 2008 incident, where the MBTA sought a legal remedy to silence the MIT students, the agency is now more cooperative. Harris believes that the authority’s past approach only drew more attention to the vulnerabilities. He remarked, “It’s great that they’re not doing that now—that they’re not shooting themselves in the foot.”
Reflecting on their achievement, Harris mused that had the MBTA not taken such drastic actions in 2008, their own research journey might never have begun.






0 Comments